Sophos
Endpoint
Sophos Intercept X: An advanced endpoint protection solution
An advanced endpoint protection solution designed to stop malware, ransomware, and other cyber threats.
Powerful EDR/XDR tools enable IT and security teams to hunt, investigate, and respond to threats.
Features are:
- Continuous security in real-time, actively preventing viruses, trojans, worms, and other malware.
- Using behavioral analysis in conjunction with machine learning to uncover and halt ransomware attacks.
- Leveraging CryptoGuard technology to prevent the unauthorized encryption of files
- Defense against attacks that exploit fileless and memory-based techniques.
- Identifying and thwarting the exploit methods employed by cybercriminals.
- Advanced threat hunting and investigation capabilities.
- Real-time visibility into endpoint activity for threat detection and response.
- Utilizes AI and machine learning for predictive analysis and proactive threat prevention.
- Protects against ransomware by identifying and stopping unauthorized encryption processes.
- Investigates and identifies the root cause of incidents for effective response and remediation.
- Centralized cloud-based management console for easy deployment, monitoring, and management of security policies.
- Controls access to websites and blocks malicious URLs to prevent web-based threats.
- Manages and controls external devices connected to endpoints to prevent data loss.
- Isolates compromised endpoints from the network to contain threats.
Network
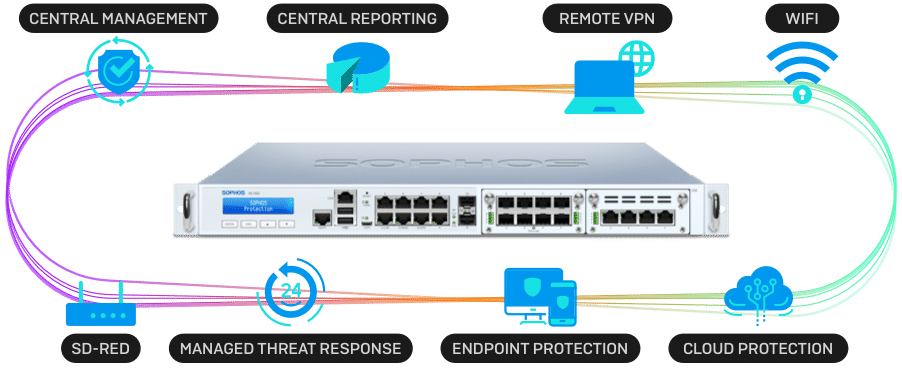
Sophos Firewall: A next-generation firewall
A next-generation firewall that provides network security, web protection, and email security features.
Sophos Firewall and XGS Series appliances, equipped with dedicated Xstream Flow Processors, deliver unparalleled application acceleration, high-performance TLS inspection, and robust threat protection.
The Sophos Firewall Xstream architecture is engineered to deliver high levels of visibility, protection, and performance to address some of the greatest challenges facing network administrators today.
- Provides advanced firewall capabilities beyond traditional packet filtering.
- Offers application control, intrusion prevention, and SSL/TLS inspection.
- Blocks malicious websites and provides URL filtering.
- Controls access to websites based on categories and user policies.
- Guards against email threats, including spam, phishing, and malware.
- Offers email encryption and data loss prevention (DLP) features.
- Protects the network from threats with features like IPS (Intrusion Prevention System) and network-based anti-malware.
- Manages user access policies and controls applications to enhance security.
- Facilitates secure remote access with VPN capabilities.
- Supports various VPN protocols for site-to-site connectivity.
- Utilizes cloud-based sandboxing to analyze suspicious files and URLs.
- Enhances threat detection and response by integrating endpoint and firewall security.
- Secures Wi-Fi networks with features like wireless intrusion prevention and guest network controls.
- Sophos Central management console for centralized control and monitoring.
- Provides detailed reporting and analytics on network activity and security incidents.
- Integrates security solutions for a synchronized and coordinated defense.
Security Operations
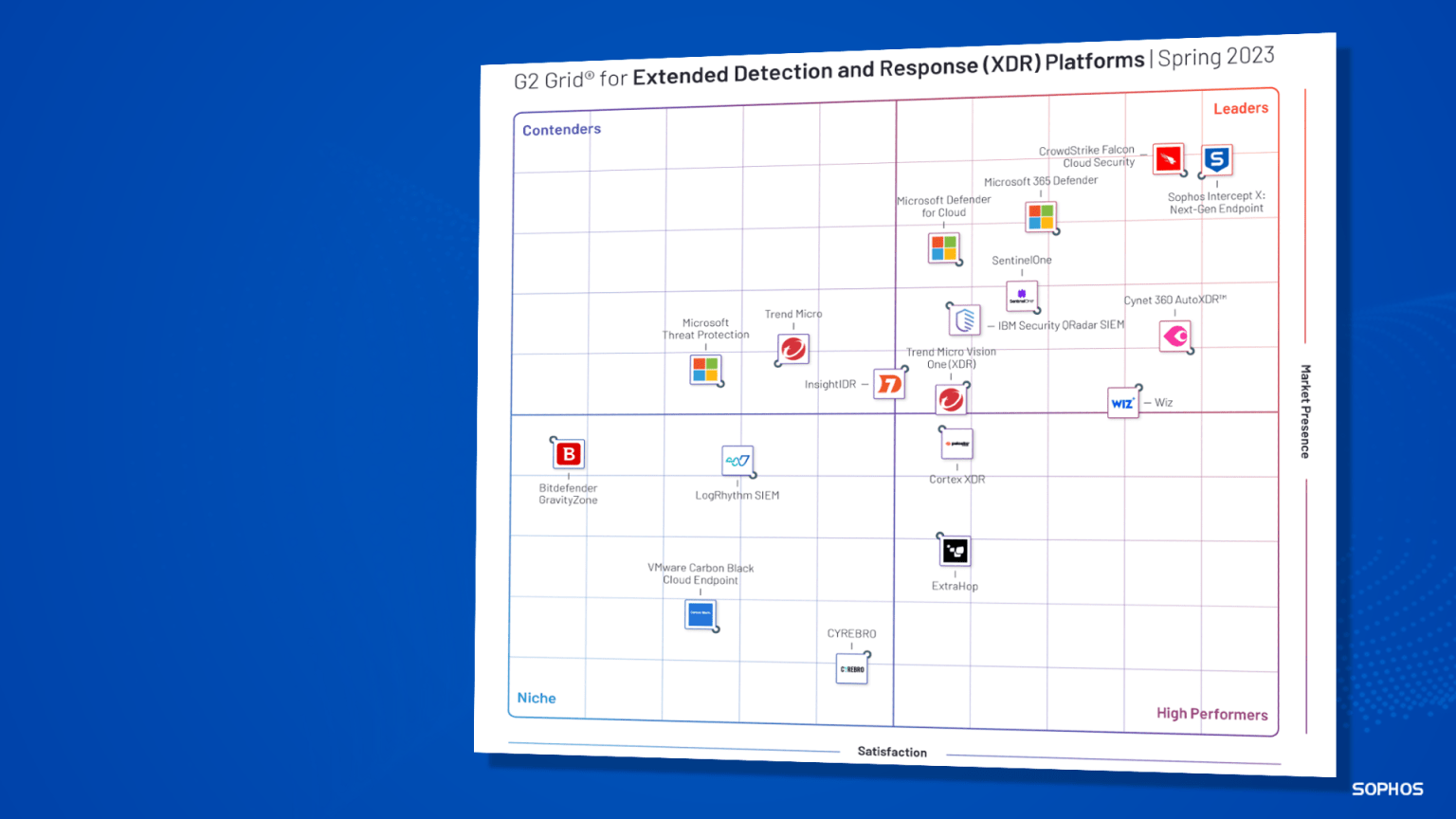
Sophos XDR:
Sophos XDR is designed to enhance threat detection, response, and investigation capabilities beyond traditional endpoint protection.
Key features include:
- Utilizes advanced threat detection technologies, including behavioral analysis, machine learning, and threat intelligence, to identify and respond to sophisticated cyber threats.
- Provides visibility into security events and incidents across various platforms, including endpoints, networks, email, and cloud environments.
- Offers incident response capabilities for swift investigation and mitigation of security incidents.
- Incorporates proactive threat hunting techniques to actively search for signs of hidden threats within an organization’s environment.
- Utilizes analytics and reporting tools to provide insights into security events and trends.
- Integrates with existing security technologies, such as endpoint protection, firewalls, and other security solutions, to provide a cohesive defense.
- Features a centralized management console for streamlined control and monitoring of security policies and events.
- Includes automation and orchestration capabilities to streamline and automate response actions to security incidents.
- Offers protection across multiple layers of the cybersecurity stack, addressing threats at different points of entry.
Sophos Intercept X with Extended Detection and Response (XDR) has been rated the #1 XDR solution by G2 users in their spring 2023 reports (March 2023)